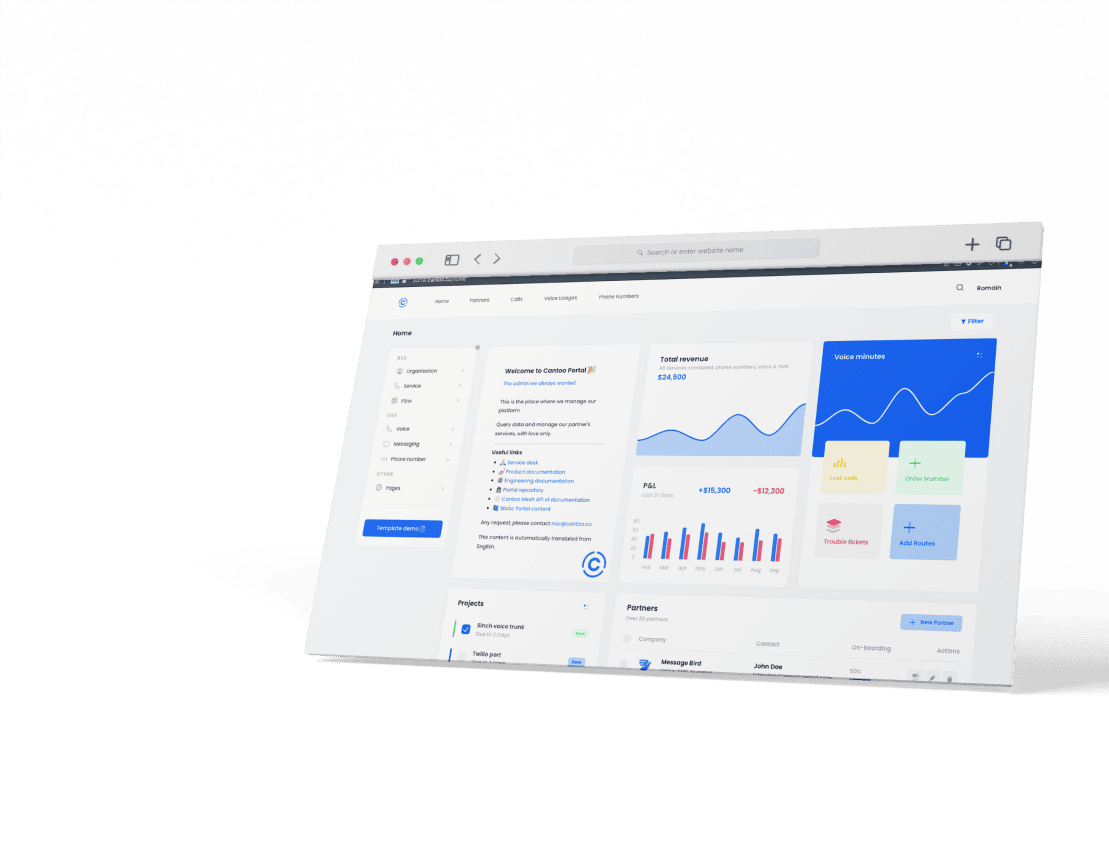
Cloud telco platform
for modern providers
Modern communication service providers use Cantoo’s hosted telecom services and APIs to create voice, video and messaging services, scale their telco operations and grow their business.Industrial Telco as a Service
White Label - Full API - Cloud - Managed
Cloud PBX
SMS Platform
Voice Routing
SMS Routing
Phone numbers
Data Connectivity
"Along with providing a reliable service, Cantoo's people are fair, straight-talking, and down to earth, which makes it very easy and enjoyable to work with. The partnership between Cantoo and Fjord Telecom has been a great success!"
"Cantoo is a stable company. They are easy to work with, provide good quality service and help us to unlock new opportunities quickly."
Our clients are rocking
See what they say about us
Industrial telcos as APIs
Create services faster than ever
- White-label solutions for seamless branding
- Fully customizable and API-driven services
- Expertly managed, cloud-based hosting by telco specialists
- Simplified integration of voice, video, and SMS into your services at scale
- No competition with your services
Why Cantoo
Modern
We offer cutting-edge telecom solutions to meet the evolving needs of businesses in today's digital age. As an independent company, we can focus on innovation and provide services that are tailored to meet the specific requirements of each client.
Cloud Expert
We are a cloud and carrier-grade telecom services expert. Our experienced team deploys and operates telecom platforms in any cloud environment, leveraging all the benefits of cloud hosting so our clients can build scalable and ultra-stable telecom services.
Compliance
We are committed to compliance with all the local regulations including GDPR and the EU Digital Act. We work with you so your telecom solutions are in full compliance with all applicable regulations, giving you peace of mind and minimizing your risk.
Redundancy
Our hosting architecture offers redundant, auto-scaling, and auto-healing capabilities to ensure optimal performance and uptime for our clients. We ensure your telecom solutions are available and operating at peak performance at all times.
White-Label
With over a decade of experience as a white-label expert, we are building the best and most flexible telecom platforms for communication service providers. With fast time-to-market, easy-to-use APIs, actionable tutorials, and dedicated support we provide our clients with the best foundation to create, operate and grow their own telecom services.
One-Stop-Shop
Cantoo is a one-stop shop for all your telecom needs. From managing voice, video or SMS platforms to hosting phone number ranges we offer a broad range of services and expertise. Our goal is to provide a comprehensive suite of telecom solutions so that you can communication service providers can focus on growing their business.
Future-Proof
We have a future-proof development roadmap that ensures our clients stay ahead of the curve in terms of telecom technology and solutions. By working with Cantoo, businesses can trust that their telecom solutions will remain relevant and effective as technology and industry trends evolve.
Registered Operator
As a registered operator in the UK, France, and Germany, Cantoo has the necessary licenses and certifications to operate as a telecom service provider in these countries. We make sure our services stay compliant and act as a reliable and trustworthy partner for your telecom needs in the EU and beyond.